Syslog
Located under Settings > Integrations, Syslog enables the configuration of result and log data forwarding to an external syslog receiver for independent, long-term storage and data analysis.
INFO: Upgrade Feature - SyslogThe ability to configure and use Syslog requires an upgraded plan. Please see https://www.sandflysecurity.com/get-sandfly/🡵 for details.
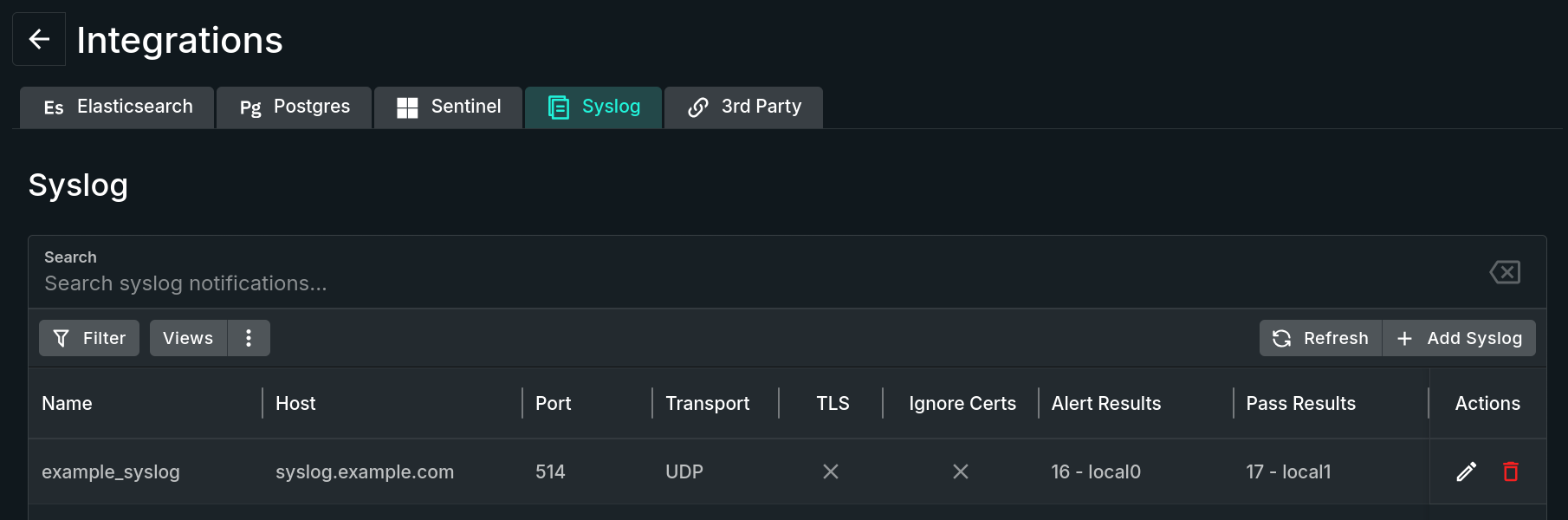
Syslog Tab
Rich Structured Data
The syslog alerts Sandfly sends are rich structured data, meaning that Sandfly sends the exact same information to the syslog server as you would see in the Sandfly UI. Therefore, you can set up Sandfly to monitor your hosts, and use your existing monitoring tools to view alerts without needing to use the Sandfly UI.
Furthermore, the data Sandfly sends contains extended attributes that allow you to search across a variety of keywords about the data, status of the alert, alert type and other key metadata.
TIP: Generate Test Alerts To See Syslog OutputOnce you set Sandfly up to send syslog output, it may be useful to generate some alerts so that Sandfly can send them to your syslog server to make sure it is working.
If you want to do a quick test, go onto a host and run the following command:
mkdir /tmp/...This will make a suspicious directory under /tmp called "..."
When you run Sandfly against this host you will see an alert activation for a suspicious directory under /tmp. This alert will be sent to your syslog server if you set it up correctly.
After you see this alert, be sure to do a
rmdir /tmp/...to get rid of the directory or you will get repeated alerts from Sandfly about the suspicious entry.
Add Syslog Form
The Add Syslog button opens a form containing the following configurable fields:
-
Name - A human-readable reference name for the syslog server.
-
Hostname - Hostname or IP address of the syslog server.
-
Transport - Select which transport method to use; options include UDP and TCP.
With the TCP option selected, the following additional fields become available:
- Use TLS - Enable to create an encrypted connection to the syslog server.
- Ignore Certificate Validation Errors - Enable to allow connecting to the syslog server even if the server certificate fails validation.
- Trusted CA Certificate(s) - Sandfly will trust certificates from public certificate authorities by default. If your syslog server uses a certificate from a private CA or is self-signed, provide the trusted certificate in PEM format in this field.
-
Port - The port of the syslog server; defaults to 514, the standard syslog/UDP port.
Syslog Entries to Send
Sandfly can send Alert results, Pass results, Audit Log entries, and Scan Error Log entries to syslog. In this section of the form, select the types of data and the syslog facility you would like Sandfly to send to this syslog server.
- Alert Results Facility - Select or disable the syslog facility used for outgoing alert results.
- Pass Results Facility - Select or disable the syslog facility used for outgoing pass results.
- Audit Log Entries Facility - Select or disable the syslog facility used for outgoing audit log entries.
- Scan Error Log Entries Facility - Select or disable the syslog facility used for outgoing scan error log entries.
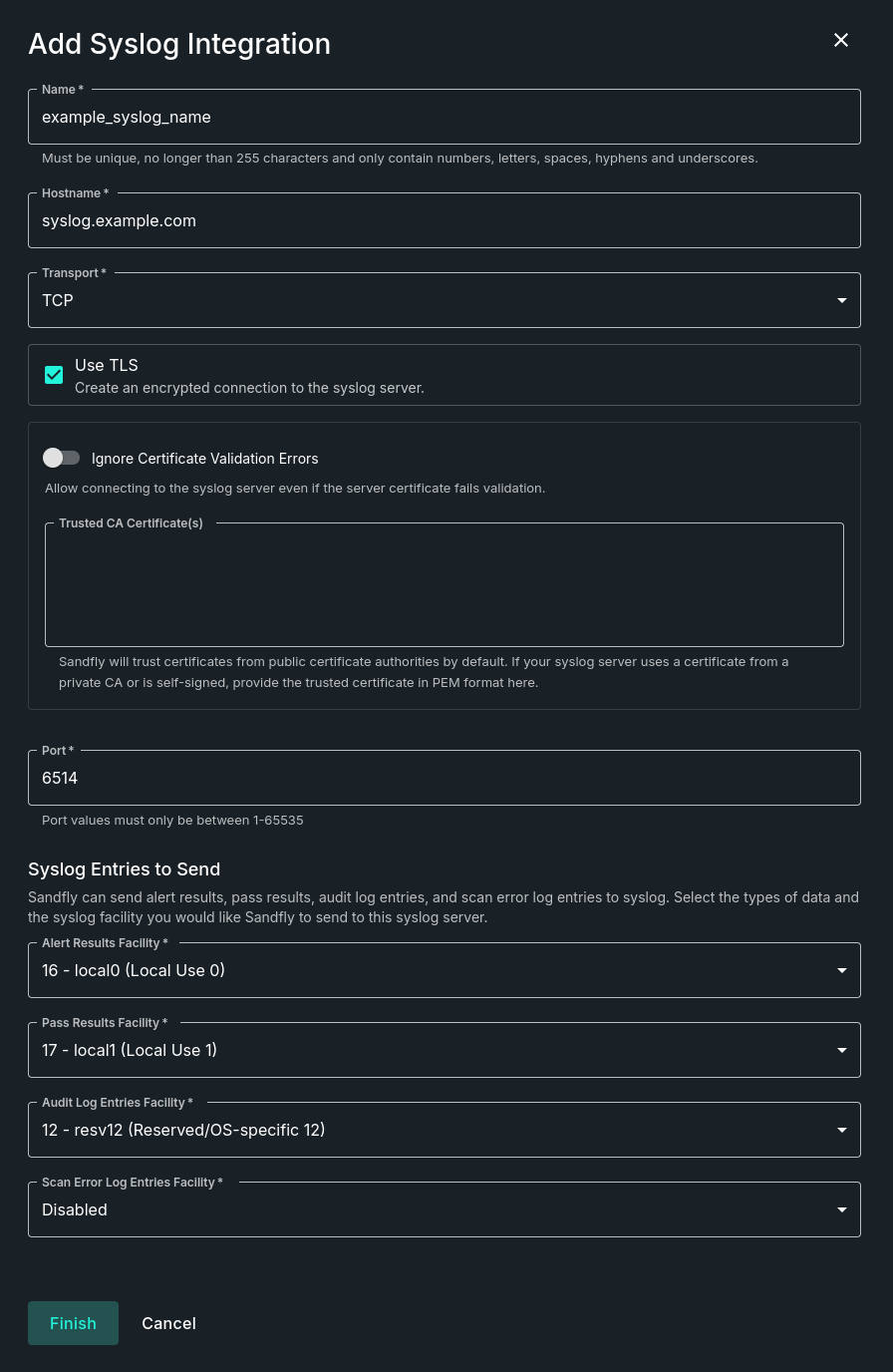
Add Syslog Form
Once the form is completed, click the Finish button to save and activate the syslog entry.
IMPORTANT: Allow Appropriate Syslog Port Access
Ensure your syslog system's packet filter allows TCP or UDP traffic from the Sandfly server based on your Transport setting, to ensure syslog data is received.
Syslog Message Priority (PRI)
Facility
- Uses the Facility associated with the configured entry type.
Severity
err("Error", numerical code 3) for Sandfly Alert results, error-level Audit Log entries, and Scan Error Log entries.warn("Warning", numerical code 4) for Sandfly Error results and warning-level Audit Log entries.info("Informational", numerical code 6) for Sandfly Pass results and informational-level Audit Log entries.
Updated 3 months ago