Theory of Operation
Sandfly provides agentless security for Linux. It does this with an innovative approach that securely connects to endpoints, deploys investigative code modules (called sandflies), and then obtains results.
Forensic Investigator
Results show either that the system is compromised in one or more ways, or show no evidence of compromise.
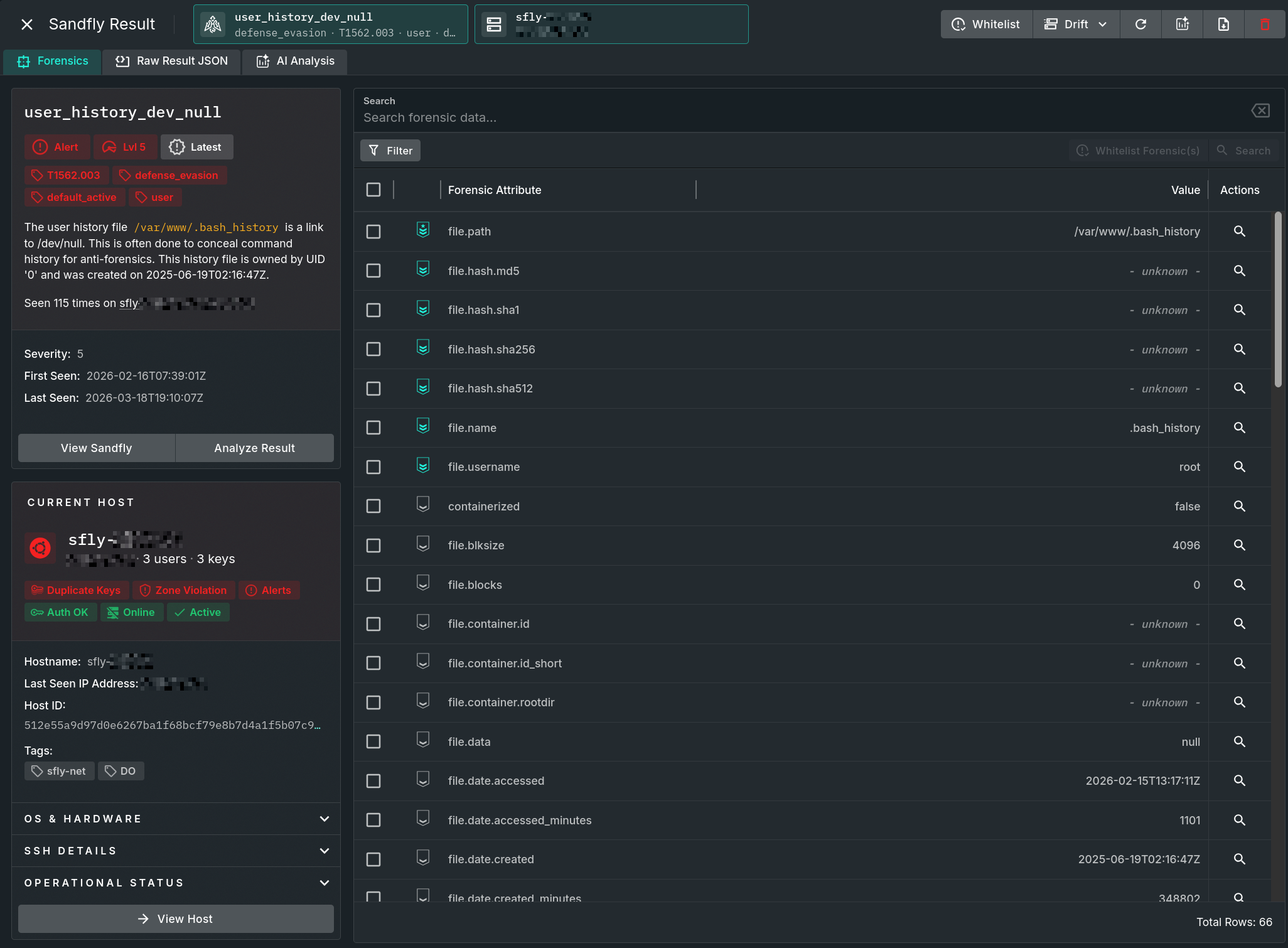
Sample Result Forensics View
Automated Security
The platform runs constantly on your network using random schedules and random selection of sandflies to hunt for threats on your Linux systems, functioning as a high-performance security investigator searching constantly for anomalies. If anything suspicious is detected, it switches roles and collects data like an expert forensic investigator to reveal exactly what is happening on the remote system.
On-Demand Investigating
Additionally, Sandfly can be used as an on-demand security investigator. During an incident, use it to search numerous Linux hosts for signs of compromise, or launch spot checks on suspected systems to collect evidence of potential activity.
Updated 3 months ago