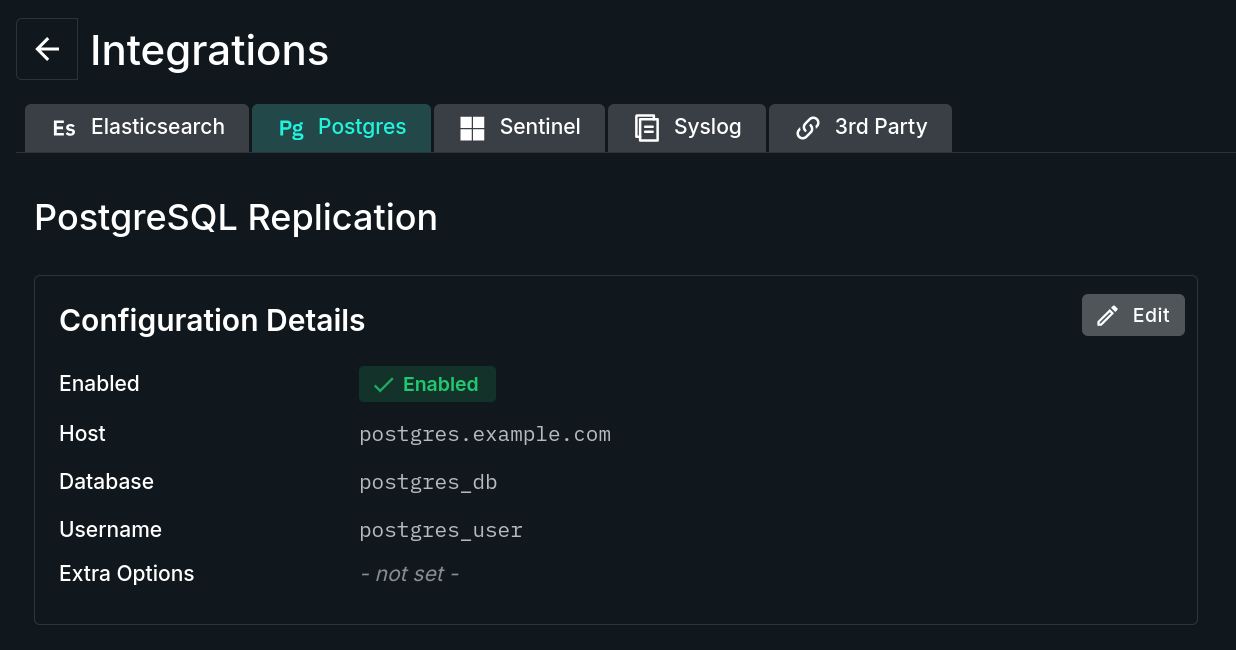
PostgreSQL Replication
Located under Settings > Integrations, PostgreSQL Replication enables the configuration of data replication to an external PostgreSQL database for independent, long-term storage and data analysis.
INFO: Upgrade Feature - PostgreSQL ReplicationThe ability to configure and use PostgreSQL Replication requires an upgraded plan. Please see https://www.sandflysecurity.com/get-sandfly/🡵 for details.
PostgreSQL Replication Tab
PostgreSQL Replication Form
The Edit button opens a form containing the following configurable fields:
- Postgres Replication Enabled - Set this to
trueto enable the PostgreSQL Replication and provide access to its settings. - Host - The network host name or the IP address of the external PostgreSQL server.
- Database - The external PostgreSQL database name for the replication data.
- Username - The external PostgreSQL database username to connect as.
- Extra Options (optional) - A space-separated,
key=valueset (e.g. "optionA=valueA optionB=valueB") of special connection options for the external PostgreSQL connection. If PostgreSQL is on a non-default port, use "port=<PORT_NUMBER>" - Password (optional) - The external PostgreSQL password associated with the specified username.
Configuring Client Certificates
The PostgreSQL client library supports the use of client certificates, however, additional steps are required to make the certificates available.
When configuring PostgreSQL replication in the Sandfly UI, there is a field called "Extra Options". Sandfly appends any provided value to the PostgreSQL connection string that is built and most PostgreSQL connection string parameters are supported. To support a client certificate, add the following space-delimited options in the Extra Options field:
sslmode='verify-full' sslcert='/pqcerts/client.crt' sslkey='/pqcerts/client.key' sslrootcert='/pqcerts/root_ca.pem'These certificate files will be loaded when Sandfly tries to connect and used for the mutual TLS authentication.
The technical complication is that those files do not exist inside the Sandfly server container. One way to make it work would be to create the pqcerts directory somewhere on the Sandfly server, then modify the start_server.sh script to add a volume mount to the docker run command, e.g. -v /path/to/pqcerts:/pqcerts, so those files will be available to the Sandfly server container at the /pqcerts path.
Updated 3 months ago